
A web application firewall (also known as a WAF) is a tool used by companies to help protect their web applications by carefully filtering the traffic from the internet to the web application. A web application can be anything from web-based mail services to online retail applications. This includes all data accessed by users through their web browsers served by an off-site server, usually hosted by a third party.
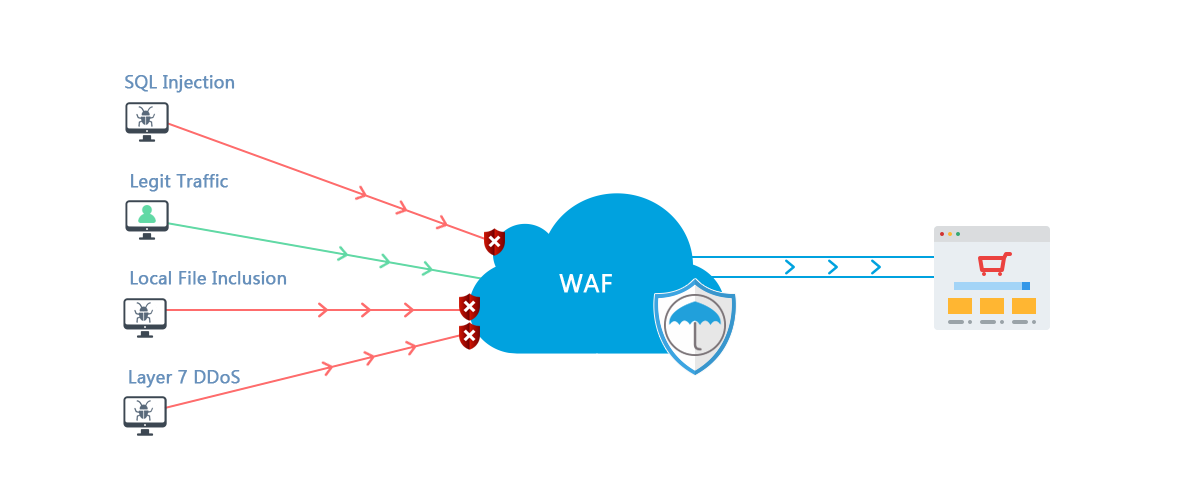
A WAF protects web applications from complex attacks, such as cross-site request forgery (CSRF) or SQL injection. It sits at the front of the web application and can analyze the HTTP traffic, moving in both directions. The WAF is designed to detect and block anything malicious attempting to access the web application. WAFs are particularly beneficial to companies with an e-commerce or finance aspect, as they are useful in preventing fraud and data theft.
There are several advantages a company can expect from using a WAF. By protecting against sophisticated, targeted attacks like cross-site scripting (XSS), WAFs can protect against severe security incursions and data theft. As well as undermining customer confidence, losing data to cyber-attacks may even mean that you are subject to regulatory penalties. A WAF can provide your company’s web administrators with the application visibility that you need to demonstrate compliance with specific regulatory standards, including GDPR.
There are several different names given to the various operating modes, but in short, a WAF can be deployed in two main ways. They can either be “Transparent” or “Reverse Proxy” If a WAF is transparent, it means that the web traffic is sent directly to the web application, so the WAF is “Transparent” between the server and the client.
A WAF that operates on a reverse proxy model acts as a proxy. The web traffic is sent directly to the WAF. At this stage, the WAF conducts its filtering operation and sends the filtered traffic to the web app. Although this might slow the loading process down, there can be benefits to this approach, including IP masking.
The definition of a WAF is quite broad – it encompasses a range of security solutions based at the application level, but which are distinct from the application itself. It can be implemented both in hardware or software. It might run in an appliance device or be part of a server running a common operating system. A WAF might be classed as a stand-alone device, or it might be integrated into other components of a network.
Although WAFs are a powerful tool for protecting web-based applications, they are not designed to provide a total security solution. They are typically most effective when used as part of a suite of cyber protection mechanisms, including network firewalls and other intrusion prevention systems. When used as part of a holistic defense strategy, they prove to be effective.