
The technological world moves at an incredibly fast rate. It can be easy to overlook certain pieces of kit, software, or process advancements simply because they come along with increasing frequency. The word “Anycast” has been bandied around relatively regularly of late, but what exactly is it, how does it compare against similar methods, and what are its associated benefits?
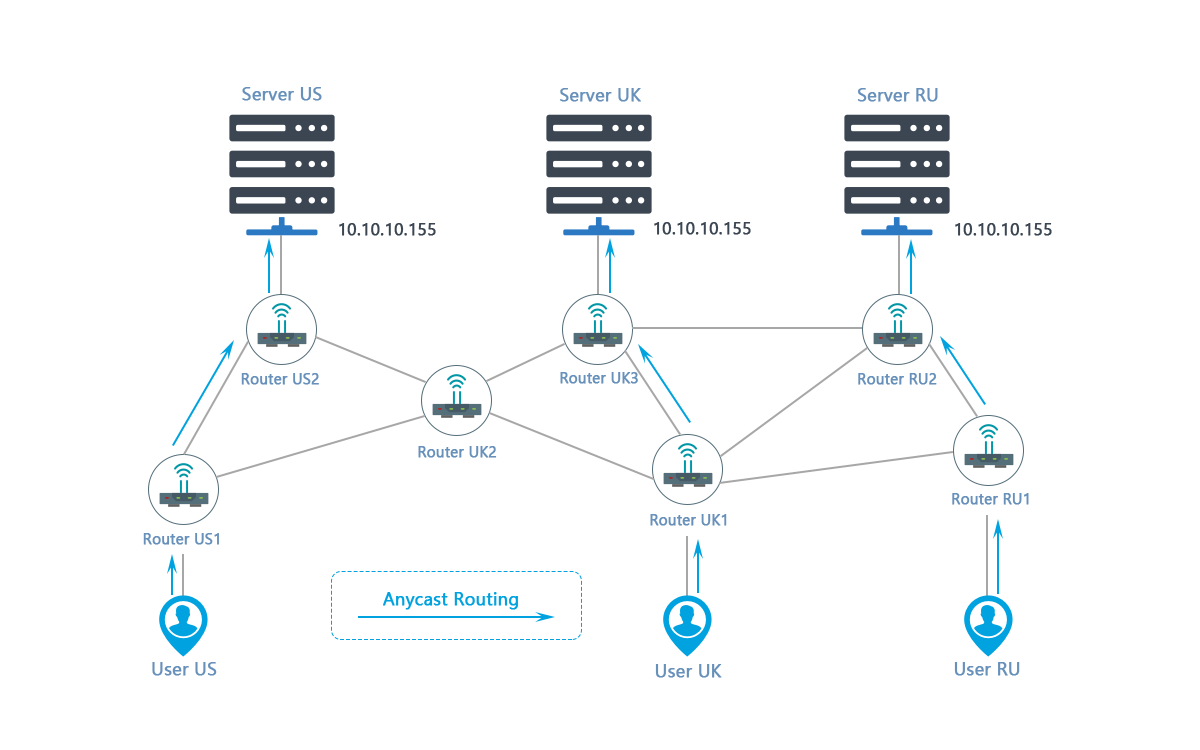
In the simplest of terms, Anycast is regarded as a “Network Addressing and Routing” technique. Its core function is to ensure that any direct traffic request can subsequently be funneled off to an array of ”Nodes” based on necessity, network capacity, or potential benefit to the user.
A content distribution network (CDN) is a network of servers, which can be localized or in various locations globally. It’s designed to give users enhanced internet surfing capabilities. With a CDN, any traffic will be pushed to a local data center (as long as it has the requisite capacity), so that all necessary actions can be taken and processes can be completed seamlessly.
Through a process known as “Selective Routing” Anycast is fully capable of carrying out and completing requests regardless of the amount of traffic or in the face of a DDoS attack.
Those that are more familiar with Anycast will be fully aware that it is frequently uttered in the same breath as “Unicast”. But why is this the case, what are the similarities, and what are the differences?
It is worth noting for the outset that the vast majority of all online activity currently operates through Unicast, which enables “One-to-One Transmissions” from one location to another. However, while Unicast is well established, it does have an inherent flaw; under certain conditions, it can be very vulnerable to DDoS attacks.
High-volume traffic can be directed to a particular node, which can cause it to get overwhelmed. An attack on the network can be designed with this vulnerability in mind to cause network confusion and denial of genuine requests.
Anycast, however, has been created with this fallibility firmly in mind. Because of this Unicast flaw, Anycast has been designed to be robust; if it is ever likely that excess traffic is expected to overwhelm a network, traffic will be rerouted to one or more capable data centers.
Anycast is designed very specifically to ensure that a specific data center does not become weakened – potentially to the point of outright collapse – as a direct result of a DDoS attack. Rather than all traffic ending up reaching a solitary data center, Anycast works to divert traffic, meaning that numerous data centers will soak up the attack, to the extent where an attack is eventually nullified completely.
Setting up an Anycast network is not simple. It needs to be crafted and subsequently implemented professionally to ensure it can be most accurate and valuable. This complexity necessitates working with an expert supplier and garnering as much knowledge as possible about what needs to be done to repel attacks and keep networks - and users - as secure as possible.